When information technology experts first sought and introduced paperless solutions for storing data in the late 20th century, the world rejoiced and the concept of a data destruction policy was pretty rudimentary at that time. There was a reason to celebrate, and there still is today – there are so many benefits to storing data digitally.
Companies or organizations can carry out transactions more efficiently. People can run personal errands like pay bills or register information with just a few mouse clicks or taps on a screen. Today, it seems as though there is nothing you can’t do online – from selling products to learning a new skill, everything is accessible on the internet.
However, for all its advantages, digital data storage also comes with one big disadvantage: running the risk of a data breach. And one of the ways that companies and individuals become vulnerable to the exploitation of confidential data (credit card fraud, identity theft, to name a few examples of data-related crimes) is when they dispose of, sell, or give away their devices.
What Is Data Destruction Policy?
A data destruction policy is a set of guidelines that specifies how an organization will retain the data collected from customers as well as all the details of how the data will be destroyed when it is no longer required. Data destruction policy must be succinct and contain precise details about the procedures to follow for data destruction, details of storage media, and the guidelines to follow at an organizational level. The data destruction policy of a company contains the following:
- Scope of the Data Destruction Policy.
- Procedures Used to Destroy Data.
- What Devices Will be Sanitized?
- Who Will Handle the Data Destruction?
- A version of Policy and updates (if any).
Every organization will have its own version that makes the most sense for its business models but these are some of the things that will be present in a data destruction policy one way or another.
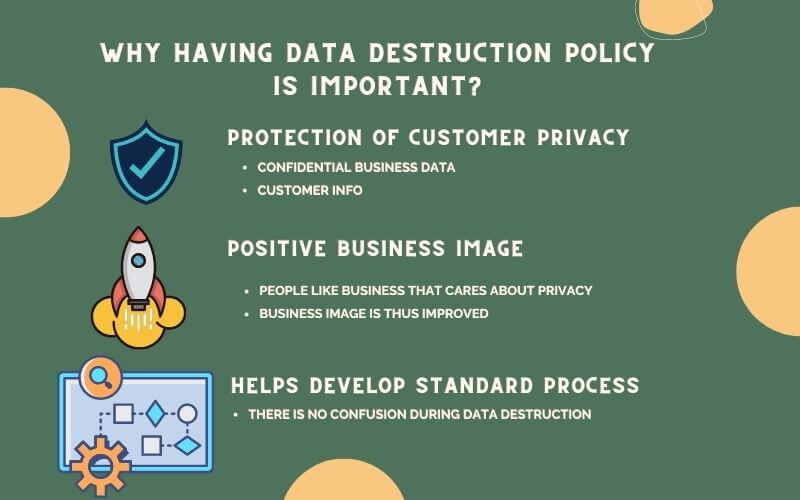
Importance of Data Destruction Policy
A data destruction policy is very important for the organization that is handling the data and its customers as well. Sensitive information related to peoples’ finances, health status, and personal info could leak out as a result of unsafe IT Asset disposal practices. This is why governments around the world have strict requirements about data retention and data destruction. If businesses do not comply with such regulations, they might pay a hefty price in loss of reputation and trust by customers. Let us explore why having a data disposal policy is important for an organization:
- Upholding Customer’s Privacy
It is just ethical and moral to handle customers’ data securely. The banking sector, the healthcare sector as well as any other company handling users’ data have a responsibility to uphold users’ privacy. A Data destruction policy effectively formulates the boundary of data retention, the scope of data destruction, and how the data sanitization will take place.
- Promoting Business Image
Having a proper data disposal policy is likely to develop a positive image of a company as customers are increasingly aware of privacy rights and choose credible businesses. Developing a data destruction policy and branding it to the people can have a tremendous positive impact on the business image and contribute to revenue accordingly.
- Methodological Approach of Handling Data.
As organizations will be fined for not upholding legislated data retention and destruction policy, it is important for an organization to have a robust set of guidelines that govern their entire data destruction process. As a result, organizations can pivot their policy swiftly if any changes in government regulations occur. Having a methodological approach to data destruction policy is, therefore, better for organizations.
Everything from laptops, phones, hard disks, servers, backup tapes, and other storage media can be picked apart to retrieve their previous users’ sensitive data. If you plan to get rid of any personal equipment or are considering IT equipment disposal, make sure they go through secure data erasure first.
What is secure data erasure? What happens when the data in your devices or equipment don’t get wiped? In this article, apart from data destruction policy, also learn about secure data erasure or media sanitization and instances where companies or organizations suffered from data breaches.
Data Erasure and Its Significance in a Data Disposal Policy.
Also referred to as data wiping or data destruction, data erasure refers to the software-based process of overwriting data to completely destroy all data stored in hard drives, servers, and other digital media. The process renders the data undiscoverable or irrecoverable. The equipment maintains full functionality after the data wipe which is important for organizations wanting to reuse their devices.
Although used synonymously, data erasure and data destruction are a bit different. While data erasure is a process of removing data backed by a certificate, data destruction may or may not be backed by a certificate.
Data erasure is a very important element of data destruction policy and constitutes a major portion of any data disposal policy in different organizations. That’s why data destruction policy cannot be discussed without highlighting secure data destruction.
Results of Not Following Proper Data Destruction Standards
Perhaps the importance of a data destruction policy can be known by analyzing the consequences of not having one. Not following proper data destruction standards can have severe implications for the business and everyone involved. Let’s see some real-world examples of the organizations that suffered complications due to not having an effective data disposal policy or not following such policies even after having one.
University of Florida, USA
In 2008, an assistant professor of plastic surgery at the University of Florida College of Medicine-Jacksonville saved photos of his patients and files containing their personal information (names, dates of birth, social security numbers, Medicare numbers) on his computer.
Later on, the doctor gave this computer to a family he was friends with without submitting the computer for secure data erasure. Thankfully, the computer’s recipient did not exploit the data found on the computer. All of the doctor’s patients’ data was permanently erased after the friend had the computer’s operating system replaced.
Even though the data was not exploited, the doctor was found to violate university policy for storing the data on his computer instead of a secure university-issued server and for transferring the unit to another person.
Agbogbloshie, Ghana
Agbogbloshie is one of the world’s biggest digital dumping grounds. Electronic waste from countries like the US, the UK, and Germany pile up there.
As the saying goes, one man’s trash is another man’s treasure. Young schoolboys scour the area for scraps of metal they can use. They burn old foam on top of computers to melt away the plastic and expose pieces of copper and iron, which they sell.
Others, like members of organized crime rings, comb through hard drives to recover data that is still stored there. A group who investigated this activity took a few of these hard drives to Ghana’s Regent University where a computer scientist read what the drive contained. He was later able to retrieve sensitive information: personal information, credit card data, records of online transactions, and more. In a separate incident, data from the US government was also recovered there.
This investigation was performed in 2011. Today, Agbogbloshie still remains to be a major dumpsite for the West’s e-waste.
Vancouver, Canada
In 2018, a Vancouver-based computer retailing company called NCIX caught fire when their used servers and hard drives were advertised on Craigslist, exposing thousands of customer and employee data. The privacy breach appeared to have occurred after NCIX closed its stores and retired its old servers. After NCIX went bankrupt in December of the previous year, its inventory was auctioned off, but it clearly did not go through a data wipe.
The pieces of equipment — some 300 desktop computers, 18 DELL Powerage servers, and two backup Supermicro servers running StarWind iSCSI Software — were then advertised on Craigslist. The servers had a price tag of up to $1,500 CAD.
Customer credentials, invoices, photographs of customer’s IDs, addresses, email addresses, phone numbers, IP addresses, and more sensitive information were found on these pieces of data storage equipment. NCIX failed to wipe or encrypt the data they had. The fiasco resulted in a class action lawsuit against NCIX.
Why Use IT Asset Disposal Services of Eco IT Solutions?
Regardless if you sell or dispose of your used equipment or devices, first make sure that all the data they contain are wiped. At Eco IT Solutions, we offer data protection services such as secure data erasure. We use the data erasure software Blancco to ensure your device is 100% data wiped. We can perform secure data destruction services from our facilities in NSW, VIC, QLD, or WA, or we can go to your office or data center instead.
Enquire about our services today. Call us at 02 8055 3775 or email us at info@ecoitsolutions.com. You may also message us via our website’s enquiry form.
FAQs
Why Should Data be Destroyed?
Simply put, once the data has served its purposes, it is best destroyed to allow integrity of information. Sensitive information about people, intellectual property or trade secrets could be misused by internal or external parties, thus destroying the data is best chance for prevention.
Why Your Business Should be Using a Data Destruction Company?
Using a data destruction company, you will get a certificate of data erasure and thus shift the responsibility to a 3rd party and project your reputation. Also, not all organizations understand the technicalities of the process, or have the means and resources to do so. Using a certified data destruction company is an effective way to ensure the job is completed in a safe and secure method without incurring downtime from your IT manager or team resources.
What are Data Destruction Standards?
Data destruction standards are a set of processes developed by the scientific community/governments that specifies the technicalities of the data destruction process. Different data destruction standards are fit for different organizations, depending on your level of security needed. For example, a small business may wish to protect their IP, compared with a Military or Government body who seeks to protect the interest of a Nation.
Which Methods of Data Destruction Are Secure?
Depending on your end goal for ITAD (IT Asset disposal), you may choose a software based data erasure method which is best if you plan to either reuse or remarket the asset. Alternatively, physical destruction is best if you wish to dispose of the IT asset (or bulk assets) in a cost effective way. At Eco IT Solutions, we recommend a crush & shred method to guarantee that data is irrecoverable. If you are still concerned about data security, we recommend having the drives destroyed either on-site at your premises or sending a company representative to witness the destruction at our facility. We no longer recommend degaussing as it does not apply for all data bearing devices, in some ways we believe this is somewhat of a redundant method of erasure.
How to Determine if we Need On-site or Off-site Data Destruction ?
If your organization has a self-determined security concern for data bearing assets, we recommend on-site data erasure or data destruction. This method may incur more costs, but you have the certainty of ensuring all HDDs, SSDs or media devices are physically destroyed or software-wiped before leaving your premises. In most cases, organizations are satisfied with off-site data destruction or data erasure after choosing a trusted and certified data destruction company.
Why do I need a Certificate of Data Destruction?
Regardless of your organization’s level of security concerns, you should always insist on receiving a certificate of secure data destruction or secure data erasure. This is to ensure the contracted company has completed the secure data destruction process and thus shifting liability to them.
One thought on “Data Destruction Policy: Why You Should Care?”
Comments are closed.



Ways Data Destruction Services Can Save You | Eco IT Solutions | Eco IT Solutions
[…] decide to sell that server as an asset management strategy, you have to have these servers undergo data erasure first. Otherwise, the data found in these servers will be easily accessed and may even be sold to […]
September 21, 2020